Social engineering attacks work better than ever, as people cause 82% of all data breaches. These deceptive tactics spread faster across organizations, and they have become harder to spot.
Verizon’s 2022 report shows these manipulative techniques remain in the top three attack patterns since 2017. Phishing incidents doubled in 2020 compared to the previous year. This happened more often when people stayed home and felt emotional stress during lockdowns. The data shows external threat actors launched every social engineering attack incident. They wanted money (89%) or aimed to spy (11%). Understanding these common social engineering attack types is vital now. This applies to senior executives who face sophisticated whaling attempts and employees who risk sharing sensitive information. Let’s get into the seven most dangerous examples of social engineering attacks you should prepare for in 2025.
Phishing Attacks
Phishing stands out as the most common social engineering attack. It accounts for 36% of successful data breaches. Cybercriminals have become smarter with their techniques. Their deceptive attempts now go way beyond the obvious grammar mistakes and suspicious links we saw before.
Phishing attack overview
Phishing is a type of social engineering attack that uses fraudulent communications to trick people into sharing sensitive information, downloading malware, or taking actions that put their security at risk. These attacks target human psychology instead of technical weaknesses. Most successful online attacks start when someone clicks a malicious attachment in an email, direct message, or social media post.
The numbers tell a scary story:
- Phishing plays a role in 36% of successful data breaches
- Security incidents from phishing make up over 80% of all reports
- A phishing breach costs $4 million on average
- Since ChatGPT launched in 2022, phishing attacks have jumped by 4,151%
Phishing becomes extra dangerous because it adapts so well. Mass phishing campaigns blast emails to countless addresses hoping some will work. More targeted approaches like spear phishing and whaling zero in on specific people or executives using personal details about them.
How phishing attacks work
Phishing follows a clear pattern of deception and manipulation. Attackers pretend to be trusted sources—banks, service providers, coworkers, or executives—to make you feel safe. Their messages usually contain:
- A convincing story or excuse (account problems, suspicious activity, urgent requests)
- Psychological triggers (fear, curiosity, urgency, or greed)
- A call to action (clicking links, opening attachments, providing credentials)
Two main technical methods stand out:
Malicious attachments: These files look harmless—usually PDFs (47%), ZIP files (11%), or documents (11%)—but install malware when opened.
Malicious links: Each email contains about 3.9 hyperlinks. These take victims to fake websites that look just like real ones and steal login details or download malware.
Psychology plays a huge role. Phishers know how to exploit human nature. Cisco explains it well: “Phishing is effective because it exploits the vulnerabilities of human nature, including a tendency to trust others, act out of curiosity, or respond emotionally to urgent messages”.
Cybercriminals keep getting better at their craft. AI shows up in 73.8% of phishing emails in 2024, making them harder to spot. They also use polymorphic features in 76.4% of attacks, which means making tiny changes to similar emails to slip past security systems.
Real-life phishing example
The Colonial Pipeline attack in 2021 shows just how devastating phishing can be. One stolen password from a phishing attack led to ransomware that shut down almost half of the U.S. East Coast’s oil supply for a week.
The damage was huge:
- Colonial Pipeline had to pay $4.4 million in ransom
- Multiple states ran short on fuel
- A single successful phishing attempt compromised critical infrastructure
Facebook and Google faced their own crisis between 2013-2015. A Lithuanian hacker sent spear phishing emails that looked like they came from their manufacturing partner (Quanta). This trick convinced employees to make fake payments. The scam cost these tech giants $100 million, though they got back about $49.7 million later.
These stories show why phishing opens the door for most complex cyber attacks. Research from Verizon backs this up – the human element shows up in 68% of breaches, and phishing kicks off 80-95% of these cases.
Pretexting
Pretexting stands out as one of the most dangerous social engineering attacks. It needs more planning and research than simpler methods. Verizon’s analysis shows pretexting in 27% of social engineering breaches, which poses a major threat to organizations and people alike.
Pretexting attack overview
A pretext attack happens when attackers create fake scenarios to trick victims into sharing sensitive information or taking unusual actions. This attack is different from regular phishing because it’s more sophisticated and personalized. While phishing targets many people at once, pretext attacks use carefully crafted stories and keep victims engaged longer to build trust before striking.
Every pretext attack has two main parts:
- The character: The role attackers play—they often pretend to be trusted figures like executives, IT support staff, or service providers
- The situation: The made-up story that explains why they need information or action from the victim
These attacks are particularly dangerous because they target human psychology rather than technical weak points. Criminals take time to study their targets. They collect information from public sources, data breaches, and social media to create believable scenarios. Research shows hackers can build a convincing story after just 100 minutes of online digging.
How pretexting manipulates victims
Attackers follow specific steps to build trust and manipulate their victims. They start by gathering background information about targets from public databases, social media, and company websites. Then they create a story that fits their victim perfectly.
The mind games begin when attackers build trust and authority through various tricks. They might act as executives, coworkers, or service providers while playing on emotions like fear, urgency, or helpfulness. They make their deception more believable by faking email addresses and phone numbers.
Pretexting works by exploiting these human traits:
- Trust tendencies
- Low perception of threat
- Response to authority
- Susceptibility to react emotionally
After gaining trust, attackers ask directly for sensitive details or actions that help them. This could mean asking for passwords, access rights, financial information, or money transfers.
Ground pretexting example
Ubiquiti Networks lost about USD 46.70 million in 2015 when criminals posed as high-level executives. They tricked employees into sending money to fake bank accounts [38, 39].
MacEwan University faced a similar fate in 2017. A scammer pretending to be a contractor fooled staff through email and stole almost USD 9.00 million by asking to update payment details.
The 2006 Hewlett-Packard scandal shows another side of pretexting. HP hired private investigators to find board members who leaked information to journalists. These investigators pretended to be board members and used their Social Security numbers to get phone records from phone companies. This scandal forced HP’s chairwoman Patricia Dunn to resign and face criminal charges.
A 2024 case shows how pretexting now uses deepfake technology. Attackers created realistic copies of several senior managers, including a chief financial officer, from public video and audio clips. They used a fake video call to convince an employee to transfer about HKD 200 million (USD 25.6 million).
The Federal Trade Commission reports that imposter scams, including pretexting, top the fraud list. These scams caused losses of USD 2.7 billion in 2022 alone.
Baiting
Baiting stands as one of the oldest social engineering tactics that still works amazingly well. It taps into human curiosity and greed to trap victims. Research shows this technique remains widespread because it exploits our natural psychological weaknesses. This makes it sort of hard to get one’s arms around, even with better technology.
Baiting attack overview
Baiting tricks victims through attractive offers or rewards that end up making them download malware or give away sensitive information. Unlike other attacks, it directly plays on people’s desire to get free stuff or information, or their natural curiosity. The main goal is to manipulate people into actions that put their security at risk.
This technique shows up in three main forms:
- Clickbait: Uses attention-grabbing ads or headlines to trick users into providing credentials or downloading malware
- Spear baiting: Targets specific individuals or organizations with customized lures based on reconnaissance
- Physical baiting: Uses tangible items like infected USB drives placed where targets will find them
Baiting attacks follow a clear pattern: they grab the target’s attention, entice them to take risky actions, and then exploit their compromised position. These attacks are especially dangerous because victims actively participate in their own downfall by choosing to interact with the bait.
How baiting tricks users
Baiting works by exploiting predictable human behaviors through psychological manipulation. Attackers create scenarios that trigger emotional responses or appeal to our basic desires.
Attackers often use psychological triggers like urgency (“Only 5 gift cards remaining. Claim immediately!”), lack of resources (limited-time offers that make you fear missing out), and social proof (fake testimonials about successful rewards). These tactics bypass our logical thinking and push us toward quick decisions.
Digital baiting often involves emails or websites that promote tempting offers like free downloads, discounts, surveys with rewards, or clickbait headlines. Physical baiting works just as well – attackers leave infected USB drives in parking lots, office lounges, or other spots where curious employees might pick them up.
The scariest part about baiting is that it doesn’t need advanced technical skills. It relies on understanding human psychology and creating believable scenarios that make victims willingly act against their interests. This makes baiting attacks available to more threat actors compared to complex technical exploits.
Real-life baiting example
A fascinating real-life example comes from Google’s USB experiment in 2016. Researchers dropped 297 USB drives across a university campus. The results shocked everyone – 48% of these drives were picked up and plugged into computers. This experiment shows how effective physical baiting attacks can be, even in places where you’d expect people to be more careful.
Another worrying case happened in 2018 when several U.S. state and local government agencies received CDs infected with malware. These CDs contained Mandarin language Microsoft Word files with malicious Visual Basic scripts. The recipients didn’t open these files, but the incident shows how baiting targets government institutions.
Physical baiting has evolved to include QR codes in public places or mail. During the COVID-19 pandemic, attackers sent USB drives that looked like Department of Health and Human Services mail about updated guidelines. They wanted people to plug them into their workstations. A second wave came disguised as Amazon gift boxes with $50 Best Buy gift cards, which led to ransomware infections.
Security technologies keep improving, but baiting attacks thrive because they target the weakest link in any security system – human behavior. Organizations need to address both psychological and technical aspects of security. Until then, baiting will remain one of the most dangerous social engineering techniques.
Quid Pro Quo
The Latin phrase “quid pro quo” means “something for something,” which perfectly describes how attackers trick people by offering services in exchange for sensitive information. This deceptive technique works because it targets basic human instincts of reciprocity and trust. Even security-conscious people fall victim to these attacks.
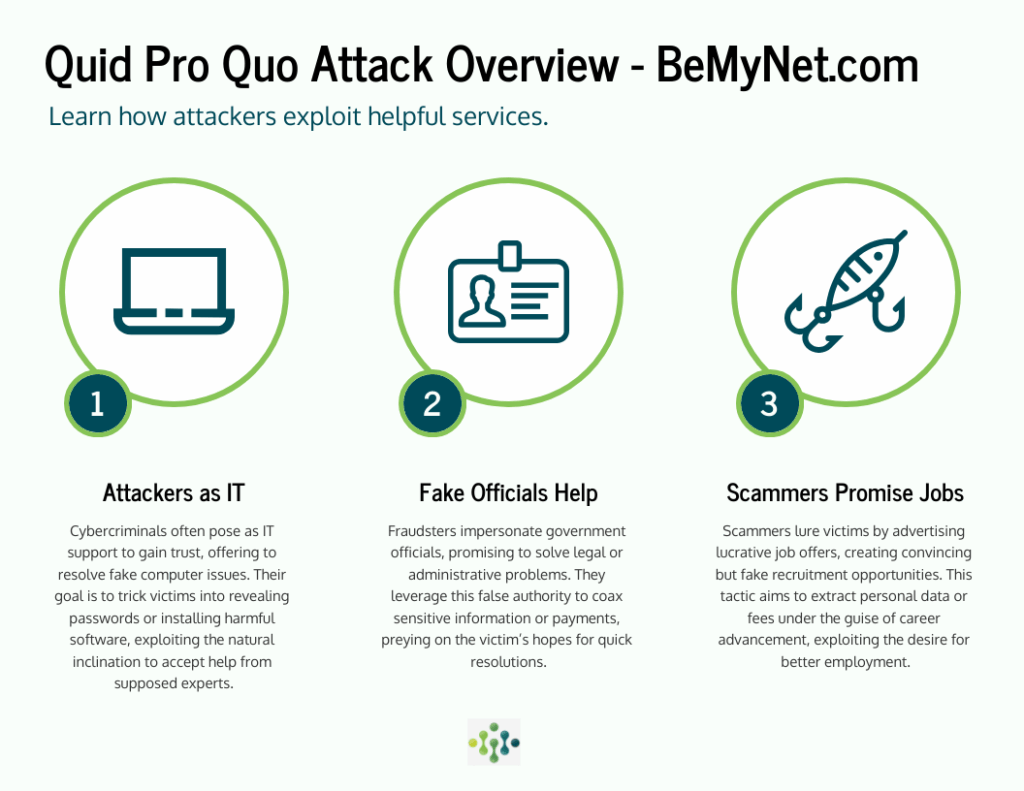
Quid pro quo attack overview
Cybercriminals execute quid pro quo attacks by promising victims helpful services or benefits to get sensitive information like login credentials, personal details, or system access. These attacks differ from baiting, which offers physical goods, as they focus on providing services. The danger lies in their legitimate appearance. Attackers pose as helpful individuals and exploit people’s natural tendency to return favors.
Common quid pro quo scenarios include:
- Attackers who pretend to be IT support staff and offer to fix non-existent computer issues
- Fraudsters who act as government officials and offer to resolve disputes
- Fake recruiters who dangle attractive job opportunities
- Technical support scams that promise to remove malware or speed up computers
The insidious nature of these attacks shows when attackers actually deliver their promised help. They build trust before asking for something more valuable. They might speed up someone’s computer while secretly installing malware or stealing sensitive data.
Psychological tactics used
Attackers use sophisticated psychological manipulation to bypass rational thinking. They create a sense of debt in their targets by offering help, which makes victims more likely to comply with future requests. This strategy uses the deeply rooted principle of reciprocity in human behavior.
These attacks also involve:
- Authority impersonation: Criminals pose as trusted figures like IT specialists or executives because people naturally trust and follow authority figures
- Trust building: Attackers prove their credibility by showing expertise or giving small amounts of real help
- Urgency creation: They use time-sensitive offers or threats to create stress and force quick decisions
- Exploitation of desires: They target human wants, such as fixing annoying technical problems or getting benefits
Research shows these psychological techniques substantially increase compliance rates. Tech support scams have become one of the most common forms of quid pro quo attacks. The FBI reports these scams ranked as the third costliest cybercrime in 2023, with losses exceeding $900 million.
Ground quid pro quo example
A chilling example shows how a staff member got a call from someone claiming to be IT support. The caller said they detected suspicious activity on the account and threatened immediate suspension if not addressed. The staff member panicked and accepted the caller’s help.
The attacker guided the victim through steps that gave them remote computer access while pretending to be a technician. They “fixed” a fake issue and installed hidden malware. Over several weeks, the malware collected login credentials, which the attacker used to access and empty the victim’s bank account.
The hacking group Lazarus pulled off an even more dramatic heist in 2022 using quid pro quo tactics. They created fake recruiter profiles on LinkedIn and tricked a senior engineer from Sky Mavis (the company behind Axie Infinity) into fake job interviews. The engineer downloaded what looked like a job offer file, but it contained spyware that gave attackers access to the blockchain network. The result was devastating—they stole $617 million in cryptocurrency, making it one of the largest cryptocurrency heists ever recorded.
Watering Hole Attacks
Watering hole attacks stand out in the predatory world of cybersecurity threats. These attacks use a patient, strategic approach that mirrors predators in nature who wait near water sources for their prey instead of hunting them down.
Watering hole attack overview
Threat actors launch watering hole attacks by targeting websites their victims visit frequently. Cybercriminals plant malicious code on trusted websites to ambush users who visit them. This strategy works well because users tend to lower their defenses on familiar sites.
These attacks usually aim to:
- Steal data and conduct espionage
- Access networks without authorization
- Create entry points for bigger attacks
Security teams find it hard to detect watering hole attacks. Attackers can breach even the most secure organizations by targeting their employees, partners, or vendors who might have weaker security measures. The use of legitimate websites makes blacklisting nearly impossible, and attackers craft their malware to slip past antivirus software.
How attackers compromise trusted sites
Attackers follow a careful plan to execute watering hole attacks. They start by mapping websites that their target organizations visit often, such as conference sites, professional forums, or government portals. The next step involves searching these sites for security gaps.
After finding weak spots, attackers inject harmful code into these legitimate websites. The malicious code comes in several forms:
- JavaScript or HTML code that sends users to dangerous sites
- Downloads that infect devices without user action
- Fake update prompts that trick users into downloading malware
The “Living off Trusted Sites” approach lets attackers use popular services like GitHub, Google Drive, or Microsoft OneDrive. These platforms have built trust and face minimal restrictions or monitoring. This makes it very hard to spot and trace malicious activities.
Real-life watering hole example
The Department of Homeland Security revealed a major breach in 2018. Foreign hackers had broken into hundreds of secure U.S. electric utility networks through watering hole attacks. The attackers gained access to control rooms and could have caused nationwide power outages.
The United Nations network suffered a breach in 2016 when attackers targeted the International Civil Aviation Organization (ICAO). Forbes.com became another target in 2014, with attackers focusing on visitors from financial services and defense sectors.
Johns Hopkins Center’s “Live Coronavirus Data Map” became a target in 2021. Attackers used it to spread malware across the country. This shows how attackers adapt their methods and target sites that draw heavy traffic during major global events.
Whaling (Executive Phishing)
Whaling attacks stand at the top of social engineering threats, preying on organizations’ “big fish.” These attacks target high-profile executives who have access to valuable assets. Their personalized nature makes them devastating when they succeed.
Whaling attack overview
Whaling represents a sophisticated phishing variant that zeros in on senior executives or C-level employees to steal money, sensitive information, or get unauthorized system access. Unlike standard phishing campaigns that cast wide nets, whaling messages come carefully crafted to fool even security-savvy leaders. Attackers usually pose as trusted individuals or groups, often mimicking another senior executive from the same organization.
Whaling stands apart from other social engineering attacks because of its laser-focused targeting and customization. The process needs extensive research before execution. Attackers might spend weeks preparing the perfect deceptive message. Though complex, successful whaling attacks can bring huge payoffs—making them worthwhile for cybercriminals.
How whaling targets high-level executives
Cybercriminals launch whaling attacks through several sophisticated techniques like email spoofing, content spoofing, and detailed social engineering. They start by doing thorough research on their targets and collect information from:
- Public social media profiles
- Company websites and press releases
- Executive interviews and presentations
- Financial disclosures and regulatory filings
Armed with this information, attackers create highly personalized messages that exploit the executive’s authority and access privileges. They use psychological manipulation by creating urgent scenarios that push for quick action without proper checks. Messages often copy the writing style of known contacts and include real business details to look more credible.
Psychological manipulation usually involves creating fake crises that bypass standard security measures. Attackers might first use basic phishing to access internal communications, which helps them learn personal details and know when executives are away.
Real-life whaling example
Successful whaling attacks can cause massive financial damage. Austrian aerospace parts manufacturer FACC lost USD 47 million in 2016 when cybercriminals fooled their finance department by pretending to be the CEO. This catastrophic breach led to both the CEO and CFO losing their jobs.
Snapchat became a victim in 2016 when scammers posed as CEO Evan Spiegel and asked HR for employee payroll information. Seagate Technology faced a similar fate when a whaling attack tricked an executive into exposing W-2 tax forms of about 10,000 current and former employees.
Wire transfer requests in whaling attacks jumped from USD 48,000 to USD 75,000 just in the last quarter of 2020. The number of whaling attacks nearly doubled between 2020-2023, with thieves typically stealing USD 50,000 per incident.
Tailgating (Physical Breach)
Physical security breaches remain a critical vulnerability even though digital attacks dominate cybersecurity discussions. Tailgating, also known as piggybacking, happens when unauthorized individuals gain access to restricted areas by closely following legitimate users. This simple social engineering attack targets human behavior instead of technical vulnerabilities.
Tailgating attack overview
A physical social engineering attack lets unauthorized people enter restricted areas they shouldn’t access. Tailgating works differently from digital attacks because it uses face-to-face deception. People often feel uncomfortable challenging strangers. Studies show that 71% of security personnel believe their companies could face data breaches from tailgating. This makes it one of the most important security threats.
The attackers usually want to:
- Steal sensitive information or equipment
- Plant malicious devices
- Get network access
- Conduct espionage or sabotage
How tailgating bypasses physical security
Attackers use several common techniques that take advantage of predictable human behaviors. They might pretend to be delivery people carrying packages, which makes it hard to use access cards. Sometimes they claim they forgot their ID badges and ask employees to let them in “just this once”. Attackers often approach doors with their hands full so legitimate employees will hold doors open to be polite.
Mind games are the life-blood of successful tailgating. Attackers know how to use human nature – our courtesy, trust, and discomfort with confrontation. Security-conscious organizations can still be vulnerable. A security researcher showed this by getting into a FTSE-listed financial company. He pretended to have a phone conversation while following the company’s managing director into a secure elevator.
Real-life tailgating example
A 39-year-old Norwegian man boarded two flights without tickets on consecutive days in August 2024. He slipped past security at Munich Airport by following passengers who had boarding passes. Security caught him on the first day, but he managed to do it again the next day. This incident led to a review of airport security protocols.
Comparison Table
| Attack Type | Target | Goal | Technique/Method | Notable Statistics/Effect | Real-life Example |
|---|---|---|---|---|---|
| Phishing | General users | Get sensitive information or deploy malware | Fraudulent communications masquerading as trusted entities | 36% of successful data breaches; 4,151% increase since ChatGPT (2022) | Colonial Pipeline (2021) – $4.4M ransom paid |
| Pretexting | Organizations and employees | Extract sensitive data or manipulate actions | Creating fabricated scenarios with detailed backstories | Present in 27% of social engineering breaches | Ubiquiti Networks (2015) – $46.7M loss |
| Baiting | Curious individuals | Install malware or steal credentials | Offering attractive rewards or items | 48% of dropped USB drives were connected in study | 2016 Google USB experiment – 297 drives, 48% success rate |
| Quid Pro Quo | Technical users | System access and data theft | Offering services to get information | Third costliest cybercrime in 2023 ($900M losses) | Sky Mavis hack (2022) – $617M cryptocurrency theft |
| Watering Hole | Specific organizations or industries | Network infiltration and data theft | Compromising legitimate websites | Hundreds of U.S. utility networks compromised | U.S. electric utilities breach (2018) |
| Whaling | Senior executives | Financial fraud and data theft | Highly customized impersonation attacks | Average wire transfer request: $75,000 (2020) | FACC aerospace (2016) – $47M loss |
| Tailgating | Secure physical facilities | Unauthorized physical access | Following legitimate users into restricted areas | 71% of companies likely to experience breaches | Munich Airport incident (2024) – Multiple unauthorized flights |
Conclusion
Social engineering attacks keep getting more sophisticated and harder to spot. These deceptive tactics work well even as technology gets better. They target the weakest link in any security system – how people think and behave. Without doubt, every type of social engineering attack we got into plays on predictable human behaviors through tricks, lies, and psychological triggers.
Phishing tops the list of social engineering techniques and makes up 36% of successful data breaches. Pretexting just needs more homework but can cause serious damage when done right. Baiting plays on our curiosity and love for free stuff, while quid pro quo attacks use our natural desire to return favors. Attackers who set up watering hole attacks show amazing patience. They target popular websites instead of going after victims directly. As with whaling, criminals focus only on top executives who can access valuable assets. This leads to some of the most expensive breaches ever recorded. Tailgating shows us that social engineering isn’t just about digital attacks – physical security can be just as easily fooled by people.
The money lost to these attacks is huge. Colonial Pipeline paid $4.4 million in ransom. Ubiquiti Networks lost $46.7 million to fraud. Sky Mavis suffered a massive $617 million cryptocurrency theft. Learning about these attack methods has become crucial if you have anything worth protecting.
Attackers keep improving their game. They adapt to security measures and use new tech like AI and deepfakes. Security training must go beyond spotting suspicious emails to build complete awareness of all social engineering tricks. Organizations should put strong security measures in place that mix technical controls with people-focused training.
We might not be able to stop all social engineering attacks, but awareness gives us our best shot at defense. Only when we are willing to see the psychological patterns these attacks use, we can develop better skepticism and checking habits. The fight against social engineering comes down to building our human firewall. Even with all our tech advances, these attacks work because they play with basic human feelings like trust, authority, and fear.
Key Takeaways
Understanding these seven dangerous social engineering attacks is crucial for protecting yourself and your organization from increasingly sophisticated cyber threats that exploit human psychology rather than technical vulnerabilities.
• Phishing remains the top threat, accounting for 36% of successful data breaches and increasing 4,151% since ChatGPT’s launch in 2022.
• Pretexting attacks require extensive research but yield devastating results, with attackers creating elaborate fake scenarios to manipulate victims into revealing sensitive information.
• Physical security matters as much as digital – tailgating attacks exploit human courtesy to bypass physical barriers, with 71% of companies vulnerable to such breaches.
• Executives face targeted “whaling” attacks with average wire transfer requests reaching $75,000, making C-level employees prime targets for sophisticated impersonation schemes.
• Human psychology is the weakest link – all these attacks succeed by exploiting trust, authority, fear, and curiosity rather than technical flaws, making awareness your strongest defense.
The staggering financial losses from these attacks – ranging from Colonial Pipeline’s $4.4 million ransom to Sky Mavis’s $617 million cryptocurrency theft – demonstrate why comprehensive security training must evolve beyond basic email awareness to address all forms of social engineering manipulation.
FAQs
Phishing remains the most common and dangerous social engineering attack, accounting for 36% of successful data breaches. Its prevalence has increased dramatically, with a 4,151% rise since the introduction of ChatGPT in 2022.
Pretexting attacks involve creating elaborate fake scenarios to manipulate victims. Unlike broader phishing attempts, pretexting requires extensive research and planning to craft convincing narratives, making it particularly dangerous when executed successfully.
Yes, physical security breaches like tailgating remain a significant threat. In fact, 71% of companies are vulnerable to data breaches due to tailgating, where unauthorized individuals gain access to restricted areas by following legitimate users.
Executives are prime targets for “whaling” attacks, which are highly personalized phishing attempts aimed at senior leadership. These attacks can result in substantial financial losses, with average wire transfer requests reaching $75,000 in recent years.
Social engineering attacks exploit human psychology rather than technical vulnerabilities. They succeed by manipulating emotions like trust, fear, and curiosity. This human element makes them particularly challenging to defend against, as even the most sophisticated security systems can be bypassed through human manipulation.
